VMware’s Advanced Threat Prevention: Micro-Segmentation, Threat Monitoring and Response

Security is always a difficult topic to blog about because of its ever-growing complexity. There are many perspectives to be considered and varying approaches. It is also a perpetually moving target with hackers getting increasingly sophisticated and Chief Information Security Officers (CISOs) keeping up as best they can.
In this blog, we will share some of our perspectives on approaching data center security and how VMware is uniquely positioned to play a significant role.
8.9 Million Dollars in Losses
Financially motivated attacks are on the rise. It is a wide-spread problem affecting all industries. According to the FBI’s 2019 Internet Crime Report, the Internet Crime Complaint Center IC3 received 2,047 complaints identified as ransomware with adjusted losses of over $8.9 million.
According to data from the Ransomware Report, the average ransomware payment is $233,817. The below graph, by the same source, also illustrates the increase in average ransomware payments over the past few years.

The attack vectors vary over time but generally speaking are either phishing emails, compromised Remote Desktop Protocol (RDP)/Active Directory credentials, or software vulnerability exploits. The below image shows the attack vectors and the top ransomware groups that use them.

Protecting against these attacks is a multi-layered approach that I categorize into the below areas:

The remainder of this blog will be focused on the items depicted in orange in Figure 3. Figure 3 is not an exhaustive list; it is a collection of topics we’ve discussed with security professionals over the years. Even if you take all the above seriously, your data is still at risk. In an increasing number of cases, these bad actors lay dormant, waiting for the right time to attack. Therefore, it is critical to have full visibility into what is happening across your data center, not just at the perimeter. We should be asking who, why, what, and how from every possible angle.
Perimeter Firewalls
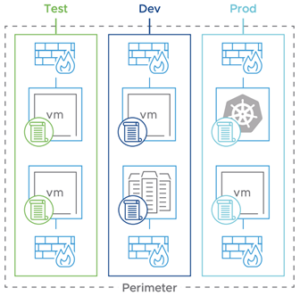
Most if not all the affected entities had perimeter firewalls. To be clear, we are in no way suggesting that perimeter firewalls are unnecessary. They’re essential, as you can see in figure 3. My point is they are not enough. For example, if an end-user clicks on a link originating from a phishing Email attack, they’re already behind the firewall. Without lateral controls, the exploit can quickly propagate throughout the network.
It is common knowledge that most data center traffic happens within the data center and behind the perimeter firewalls. This type of network traffic is also known as east/west traffic or lateral traffic instead of north/south traffic. Due to this simple fact, we need more visibility and control on east/west traffic.
VMware’s Security Vision
VMware’s persistence in its pursuit of a place in the security landscape has led to a dynamic portfolio of security solutions. VMware’s presence in the security space can be dated back to the vCloud Networking and Security vCNS days pre the Nicira acquisition. VMware acquired Nicira in 2012, re-named it NSX for vSphere or NSX-V, and set out to deliver on the promise of vNCS with an innovative hypervisor-based solution that never stood still.
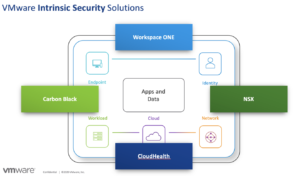
With every release, new features and functionality were introduced. Today, VMware boasts a comprehensive ‘Intrinsic Security’ strategy helping with the ‘Harden and Mitigate’ and ‘Detect and Respond’ categories presented in figure 3. The below image was unveiled at VMworld 2020 to illustrate VMware’s Intrinsic Security platform.
VMware Security Then and Now
I was first introduced to NSX in early 2014. At the time, the prominent NSX use cases were:
- Multi-site (stretched layer 2)
- It allowed users to vMotion workloads across physical data center boundaries without changing IP addresses or re-creating security policies.
- Automation (programmatic network and security object creation)
- Provided an API that could be used to manipulate networking and security constructs programmatically.
- Security (micro-segmentation) L2-L4
- Helped organizations establish a zero-trust model for east/west traffic via a distributed stateful firewall up to TCP/IP layer 4.
Since then, security has played a significant role in VMware’s acquisition and innovation efforts. Below are some notable security-related acquisitions VMware has made since 2012:
On the innovation front, VMware has also been very busy. In 2017 VMware completely re-wrote NSX to adapt it to native cloud and container workloads rebranding it NSX-T. NSX-V focused on proving micro-segmentation up to layer 4 for vSphere or KVM based virtual machines with limited support for cloud-based and containerized workloads. Below are some of the notable features and capabilities VMware has introduced to the NSX platform since 2017:
- Layer 2-7 Distributed Firewall
- Identity-Based Firewall (AD Integration)
- NSX Cloud with Support for AWS and Azure workloads
- Container Security
- Layer 7 Application Identification
- Distributed FQDN Whitelisting
- URL Filtering
- VRF Support
- Ethernet VPN (EVPN)
- Distributed IDS/IPS
- Network Detection and Response (NDR)
- Network Sandbox
These features and capabilities come together to provide VMware’s Service-defined Firewall.

NSX Advanced Threat Prevention (NSX-ATP)
NSX-ATP is a suite of security solutions that come together to provide advanced, comprehensive internal data center security. NSX ATP is focused on the below areas:
- Greater Visibility
- Advanced Malware Protection
- Reduce False Positives
- Proactive Threat Hunting
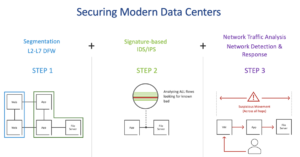
Figure 6 breaks down the adoption of NSX-ATP into three phases or steps. Below I’ll analyze all three stages and explain why I think each is important and how these solutions are differentiated in the market.

Step 1 Micro-Segmentation:
The first step in the process is to provide L2-L7 segmentation to the workloads behind the perimeter firewall. NSX does this by providing a L2-L7 stateful Distributed Firewall.
- Zero Trust – There are thousands of ports in the TCP/IP protocol used by operating systems and applications. The idea of micro-segmentation is to only allow the necessary ports and deny any communication via ports that are not required.
- AppID – Another piece to this is going beyond the port and looking at the applications themselves and allowing or denying communication-based on specific application versions. For example, you may create a firewall rule that allows HTTPS over port 443. However, you can take this a step further by restricting traffic to workloads that have TLS version 1.2 running. AppID is a compelling advancement from the NSX-V days.
- Centralized Management – NSX’s integration with vCenter allows NSX to group virtual machines based on a tag, OS Name, IPsets, or VM name. This dynamic grouping simplifies security policy creation and management across the environment.
- Differentiation:
- Hypervisor Integration: The NSX Distributed Firewall (DFW) runs in the hypervisor. This means that policy is applied outside of the guest OS, which provides better security than agent-based firewalls since these can easily be disabled.
- Efficiency: Since the NSX DFW runs in the hypervisor, it is more efficient than VM based firewall appliances that need to be managed separately.
- Simplicity: When deploying the NSX DFW, the VLAN architecture remains unchanged. You can provide L2-L7 stateful distributed firewalling for workloads residing in the same VLAN.
Step 2 Distributed IDS/IPS:
The second step in the process is to look for ‘known bads,’ I.e., signature-based workloads for east/west traffic.
- East-West IDS/IPS – As stated earlier, most attacks present at the endpoint via social engineering and then move laterally. This is why perimeter-based IDS/IPS is not enough. It is critical to catch these workloads as they attempt to propagate in the environment.
- Differentiation:
- Context-Based Signature Curation and Tuning: NSX can curate signatures for each workload because NSX has full context into the workloads and is application-aware.
- Policy Lifecycle Management: Since NSX uses dynamic group memberships, IDS/IPS policies are applied automatically when workloads are spun up. For example, you can use Windows Server 2019 as a group membership criterion. This will group all existing and future virtual machines running Windows Server 2019 into the same security group. You can then curate the signatures and only apply the Windows Server 2019 based signatures to that group.

Step 3 Network Detection and Response (NDR):
So far, we have established zero-trust and are now looking for ‘known bads’ traversing east/west across the network. What is missing is anomalous behavior detection across the network. This is important for zero-day attacks.

-
- Network Traffic Analysis: Detecting signature-based exploits is only part of the overall security posture. All attacks happen at an exposed endpoint and propagate laterally. Some of these exploits are known, but most are unknown. The focus here is to collect, analyze, and respond to never-before-seen attacks promptly.
- MITRE ATT&CK Framework Alignment: NSX NDR classifies exploits by various stages. This allows security professionals to triage the attack quickly and take appropriate action.

- Intrusion Blueprint: NSX NDR also provides an attack blueprint including compromised systems and external communication to outside networks.

- Differentiation:
- System Emulation: NSX NDR can simulate infrastructure via code. This is particularly useful when performing sandboxing activities. You can completely simulate infrastructure components, so the exploit is entirely unaware it is talking to code. This allows for NSX NDR to get more insight into these detonations.
Summary
According to data from the Ransomware Report, on average, ransomware attacks cause 16.2 days (about two and a half weeks) of downtime. An organization’s ability to stop malicious lateral movement within the datacenter could mean the difference between experiencing long term downtime or keeping the business operational. The hostile lateral movement could be well known, as we see in figure 2, in which case NSX Distributed IPS/IDS would have those signatures and could quickly stop the attack. Or it could be a zero-day attack that has not been seen before, which the NSX NDR anomalous detection would then catch. In either case, most data centers have limited lateral controls, making it difficult to detect these attacks. As VMware fans we are excited about their ongoing investment in security solutions and looking forward to VMware’s continued advances in their holistic integrated approach to cyber security.
Contact CDI’s VMware Licensing and Professional Services Team